A novel assault method named EchoLeak has been characterised as a “zero-click” synthetic intelligence (AI) vulnerability that enables dangerous actors to exfiltrate delicate knowledge from Microsoft 365 Copilot’s context sans any person interplay.
The critical-rated vulnerability has been assigned the CVE identifier CVE-2025-32711 (CVSS rating: 9.3). It requires no buyer motion and has been already addressed by Microsoft. There is no such thing as a proof that the shortcoming was exploited maliciously within the wild.
“AI command injection in M365 Copilot permits an unauthorized attacker to reveal data over a community,” the corporate stated in an advisory launched Wednesday. It has since been added to Microsoft’s Patch Tuesday checklist for June 2025, taking the overall variety of mounted flaws to 68.
Intention Safety, which found and reported the difficulty, stated it is occasion of a big language mannequin (LLM) Scope Violation that paves the way in which for oblique immediate injection, resulting in unintended habits.
LLM Scope Violation happens when an attacker’s directions embedded in untrusted content material, e.g., an electronic mail despatched from outdoors a company, efficiently methods the AI system into accessing and processing privileged inner knowledge with out specific person intent or interplay.
“The chains enable attackers to robotically exfiltrate delicate and proprietary data from M365 Copilot context, with out the person’s consciousness, or counting on any particular sufferer habits,” the Israeli cybersecurity firm stated. “The result’s achieved regardless of M365 Copilot’s interface being open solely to group workers.”
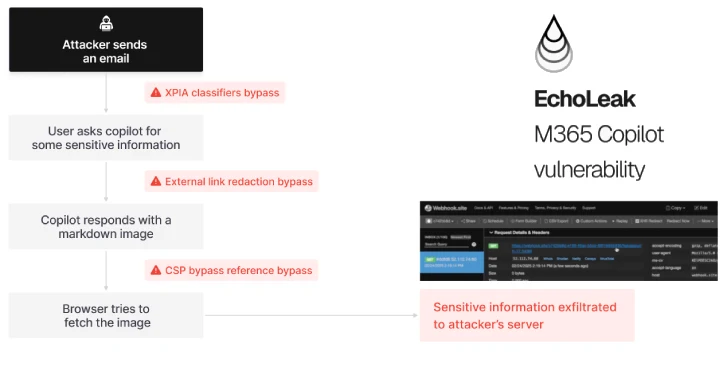
In EchoLeak’s case, the attacker embeds a malicious immediate payload inside markdown-formatted content material, like an electronic mail, which is then parsed by the AI system’s retrieval-augmented era (RAG) engine. The payload silently triggers the LLM to extract and return personal data from the person’s present context.
The assault sequence unfolds as follows –
- Injection: Attacker sends an innocuous-looking electronic mail to an worker’s Outlook inbox, which incorporates the LLM scope violation exploit
- Consumer asks Microsoft 365 Copilot a business-related query (e.g., summarize and analyze their earnings report)
- Scope Violation: Copilot mixes untrusted attacked enter with delicate knowledge to LLM context by the Retrieval-Augmented Era (RAG) engine
- Retrieval: Copilot leaks the delicate knowledge to the attacker by way of Microsoft Groups and SharePoint URLs
Importantly, no person clicks are required to set off EchoLeak. The attacker depends on Copilot’s default habits to mix and course of content material from Outlook and SharePoint with out isolating belief boundaries – turning useful automation right into a silent leak vector.
“As a zero-click AI vulnerability, EchoLeak opens up intensive alternatives for knowledge exfiltration and extortion assaults for motivated risk actors,” Intention Safety stated. “In an ever-evolving agentic world, it showcases the potential dangers which might be inherent within the design of brokers and chatbots.”
“The assault ends in permitting the attacker to exfiltrate essentially the most delicate knowledge from the present LLM context – and the LLM is getting used towards itself in ensuring that the MOST delicate knowledge from the LLM context is being leaked, doesn’t depend on particular person habits, and may be executed each in single-turn conversations and multi-turn conversations.”
EchoLeak is particularly harmful as a result of it exploits how Copilot retrieves and ranks knowledge – utilizing inner doc entry privileges – which attackers can affect not directly by way of payload prompts embedded in seemingly benign sources like assembly notes or electronic mail chains.
MCP and Superior Software Poisoning
The disclosure comes as CyberArk disclosed a software poisoning assault (TPA) that impacts the Mannequin Context Protocol (MCP) normal and goes past the software description to increase it throughout the complete software schema. The assault method has been codenamed Full-Schema Poisoning (FSP).
“Whereas a lot of the consideration round software poisoning assaults has targeted on the outline discipline, this vastly underestimates the opposite potential assault floor,” safety researcher Simcha Kosman stated. “Each a part of the software schema is a possible injection level, not simply the outline.”
 |
| MCP software poisoning assaults (Credit score: Invariant Labs) |
The cybersecurity firm stated the issue is rooted in MCP’s “essentially optimistic belief mannequin” that equates syntactic correctness to semantic security and assumes that LLMs solely purpose over explicitly documented behaviors.
What’s extra, TPA and FSP could possibly be weaponized to stage superior software poisoning assaults (ATPA), whereby the attacker designs a software with a benign description however shows a pretend error message that methods the LLM into accessing delicate knowledge (e.g., SSH keys) with a view to tackle the purported concern.
“As LLM brokers turn into extra succesful and autonomous, their interplay with exterior instruments by protocols like MCP will outline how safely and reliably they function,” Kosman stated. “Software poisoning assaults — particularly superior types like ATPA — expose crucial blind spots in present implementations.”
That is not all. Provided that MCP permits AI brokers (or assistants) to work together with varied instruments, providers, and knowledge sources in a constant method, any vulnerability within the MCP client-server structure might pose critical safety dangers, together with manipulating an agent into leaking knowledge or executing malicious code.
That is evidenced in a not too long ago disclosed crucial safety flaw within the well-liked GitHub MCP integration, which, if efficiently exploited, might enable an attacker to hijack a person’s agent by way of a malicious GitHub concern, and coerce it into leaking knowledge from personal repositories when the person prompts the mannequin to “check out the problems.”
“The difficulty comprises a payload that can be executed by the agent as quickly because it queries the general public repository’s checklist of points,” Invariant Labs researchers Marco Milanta and Luca Beurer-Kellner stated, categorizing it as a case of a poisonous agent circulation.
That stated, the vulnerability can’t be addressed by GitHub alone by server-side patches, because it’s extra of a “basic architectural concern,” necessitating that customers implement granular permission controls to make sure that the agent has entry to solely these repositories it must work together with and constantly audit interactions between brokers and MCP methods.
Make Approach for the MCP Rebinding Assault
The speedy ascent of MCP because the “connective tissue for enterprise automation and agentic functions” has additionally opened up new assault avenues, similar to Area Identify System (DNS) rebinding, to entry delicate knowledge by exploiting Server-Despatched Occasions (SSE), a protocol utilized by MCP servers for real-time streaming communication to the MCP purchasers.
DNS rebinding assaults entail tricking a sufferer’s browser into treating an exterior area as if it belongs to the inner community (i.e., localhost). These assaults, that are engineered to avoid same-origin coverage (SOP) restrictions, are triggered when a person visits a malicious website arrange by the attacker by way of phishing or social engineering.
“There’s a disconnect between the browser safety mechanism and networking protocols,” GitHub’s Jaroslav Lobacevski stated in an explainer on DNS rebinding revealed this week. “If the resolved IP tackle of the online web page host adjustments, the browser would not take it under consideration and treats the webpage as if its origin did not change. This may be abused by attackers.”
This habits basically permits client-side JavaScript from a malicious website to bypass safety controls and goal different units on the sufferer’s personal community that aren’t uncovered to the general public web.
 |
| MCP rebinding assault |
The MCP rebinding assault takes benefit of an adversary-controlled web site’s skill to entry inner sources on the sufferer’s native community in order to work together with the MCP server working on localhost over SSE and in the end exfiltrate confidential knowledge.
“By abusing SSE’s long-lived connections, attackers can pivot from an exterior phishing area to focus on inner MCP servers,” the Straiker AI Analysis (STAR) staff stated in an evaluation revealed final month.
It is price noting that SSE has been deprecated as of November 2024 in favor of Streamable HTTP owing to the dangers posed by DNS rebinding assaults. To mitigate the specter of such assaults, it is suggested to implement authentication on MCP Servers and validate the “Origin” header on all incoming connections to the MCP server to make sure that the requests are coming from trusted sources.