ASUS has launched updates to deal with two safety flaws impacting ASUS DriverHub that, if efficiently exploited, might allow an attacker to leverage the software program with the intention to obtain distant code execution.
DriverHub is a device that is designed to robotically detect the motherboard mannequin of a pc and show vital driver updates for subsequent set up by speaking with a devoted website hosted at “driverhub.asus[.]com.”
The failings recognized within the software program are listed under –
- CVE-2025-3462 (CVSS rating: 8.4) – An origin validation error vulnerability that will enable unauthorized sources to work together with the software program’s options through crafted HTTP requests
- CVE-2025-3463 (CVSS rating: 9.4) – An improper certificates validation vulnerability that will enable untrusted sources to have an effect on system conduct through crafted HTTP requests
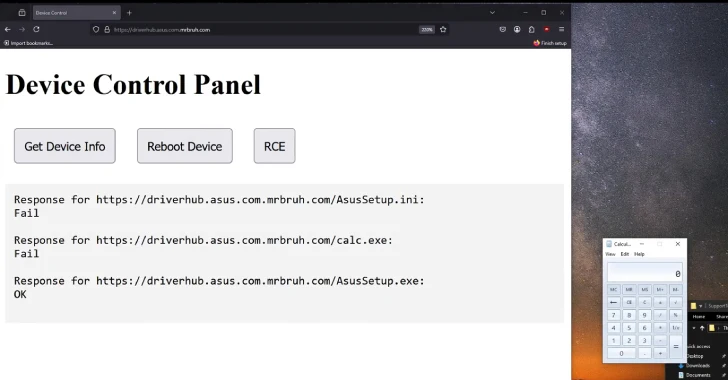
Safety researcher MrBruh, who’s credited with discovering and reporting the 2 vulnerabilities, mentioned they may very well be exploited to realize distant code execution as a part of a one-click assault.
The assault chain primarily entails tricking an unsuspecting person into visiting a sub-domain of driverhub.asus[.]com (e.g., driverhub.asus.com.
“When executing AsusSetup.exe it first reads from AsusSetup.ini, which accommodates metadata concerning the driver,” the researcher defined in a technical report.
“In case you run AsusSetup.exe with the -s flag (DriverHub calls it utilizing this to do a silent set up), it’s going to execute no matter is laid out in SilentInstallRun. On this case, the ini file specifies a cmd script that performs an automatic headless set up of the motive force, however it might run something.”
All an attacker must efficiently pull off the exploit is to create a site, and host three recordsdata, the malicious payload to be run, an altered model of AsusSetup.ini that has the “SilentInstallRun” property set to the malicious binary, and AsusSetup.exe, which then make use of the property to run the payload.
Following accountable disclosure on April 8, 2025, the problems have been mounted by ASUS on Might 9. There is no such thing as a proof that the vulnerabilities have been exploited within the wild.
“This replace contains essential safety updates and ASUS strongly recommends that customers replace their ASUS DriverHub set up to the most recent model,” the corporate mentioned in a bulletin. “The newest Software program Replace will be accessed by opening ASUS DriverHub, then clicking the ‘Replace Now’ button.”