Cybersecurity researchers have uncovered a number of safety flaws in Dell’s ControlVault3 firmware and its related Home windows APIs that might have been abused by attackers to bypass Home windows login, extract cryptographic keys, in addition to preserve entry even after a recent working system set up by deploying undetectable malicious implants into the firmware.
The vulnerabilities have been codenamed ReVault by Cisco Talos. Greater than 100 fashions of Dell laptops working Broadcom BCM5820X sequence chips are affected. There is no such thing as a proof that the vulnerabilities have been exploited within the wild.
Industries that require heightened safety when logging in, by way of good card readers or near-field communication (NFC) readers, are probably to make use of ControlVault units of their settings. ControlVault is a hardware-based safety resolution that provides a safe solution to retailer passwords, biometric templates, and safety codes inside the firmware.
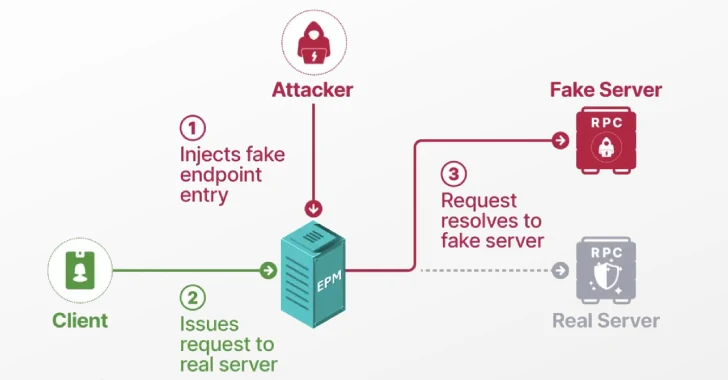
Attackers can chain the vulnerabilities, which had been offered on the Black Hat USA safety convention, to escalate their privileges after preliminary entry, bypass authentication controls, and preserve persistence on compromised techniques that survive working system updates or reinstallations.
Collectively, these vulnerabilities create a potent distant post-compromise persistence methodology for covert entry to high-value environments. The recognized vulnerabilities are as follows –
- CVE-2025-25050 (CVSS rating: 8.8) – An out-of-bounds write vulnerability exists within the cv_upgrade_sensor_firmware performance that might result in an out-of-bounds write
- CVE-2025-25215 (CVSS rating: 8.8) – An arbitrary free vulnerability exists within the cv_close performance that might result in an arbitrary free
- CVE-2025-24922 (CVSS rating: 8.8) – A stack-based buffer overflow vulnerability exists within the securebio_identify performance that might result in arbitrary code execution
- CVE-2025-24311 (CVSS rating: 8.4) – An out-of-bounds learn vulnerability exists within the cv_send_blockdata performance that might result in an data leak
- CVE-2025-24919 (CVSS rating: 8.1) – A deserialization of untrusted enter vulnerability exists within the cvhDecapsulateCmd performance that might result in arbitrary code execution
The cybersecurity firm additionally identified {that a} native attacker with bodily entry to a person’s laptop computer may pry it open and entry the Unified Safety Hub (USH) board, permitting an attacker to take advantage of any of the 5 vulnerabilities with out having to log in or possess a full-disk encryption password.
“The ReVault assault can be utilized as a post-compromise persistence approach that may stay even throughout Home windows reinstalls,” Cisco Talos researcher Philippe Laulheret mentioned. “The ReVault assault may also be used as a bodily compromise to bypass Home windows Login and/or for any native person to achieve Admin/System privileges.”
To mitigate the danger posed by these flaws, customers are suggested to use the fixes offered by Dell; disable ControlVault companies if peripherals like fingerprint readers, good card readers, and near-field communication (NFC) readers usually are not getting used; and switch off fingerprint login in excessive danger conditions.