Image this: you have hardened each laptop computer in your fleet with actual‑time telemetry, speedy isolation, and automatic rollback. However the company mailbox—the entrance door for many attackers—continues to be guarded by what’s successfully a Nineteen Nineties-era filter.
This is not a balanced strategy. E mail stays a major vector for breaches, but we frequently deal with it as a static stream of messages as an alternative of a dynamic, post-delivery setting. This setting is wealthy with OAuth tokens, shared drive hyperlinks, and years of delicate knowledge.
The dialog must shift. We should always cease asking, “Did the gateway block the unhealthy factor?” and begin asking, “How shortly can we see, comprise, and undo the harm when an attacker inevitably will get in?”
Taking a look at e mail safety by means of this lens forces a basic shift towards the identical assume-breach, detect-and-respond mindset that already revolutionized endpoint safety.
The day the wall crumbled
Most safety professionals know the statistics. Phishing and credential theft proceed to dominate breach experiences, and the monetary influence of Enterprise E mail Compromise usually outweighs ransomware. However the knowledge tells a extra attention-grabbing story, one which mirrors the decline of legacy antivirus.
A decade in the past, AV was good at catching recognized threats, however zero-day exploits and novel malware slipped previous. Endpoint Detection and Response (EDR) emerged as a result of groups wanted visibility after an attacker was already on the machine.
E mail is following the identical script. Safe E mail Gateways (SEGs) nonetheless filter spam and commodity phishing campaigns fairly properly. What they miss are the assaults that outline the fashionable menace panorama:
- Payload-less Enterprise E mail Compromise (BEC)
- Malicious hyperlinks which can be weaponized after supply
- Account takeovers utilizing stolen credentials that contain no malware in any respect
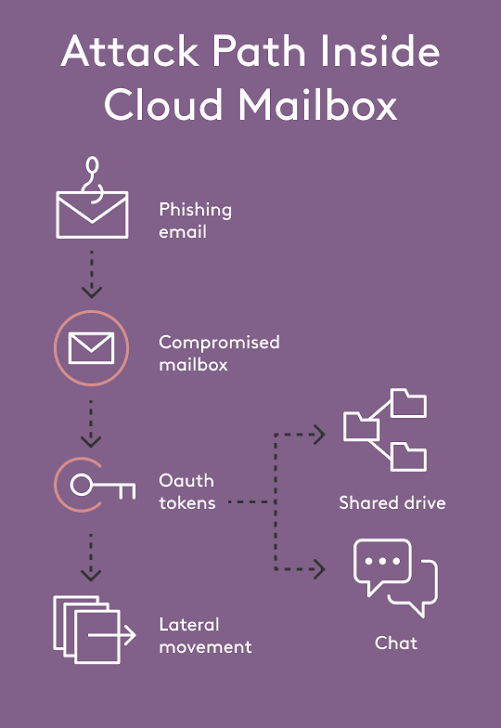
As soon as a single mailbox is compromised, the attacker positive aspects entry to a related graph of OAuth purposes, shared information, chat histories, and calendar invitations inside Microsoft 365 or Google Workspace. Transferring laterally by means of this graph hardly ever triggers one other SEG alert. The harm occurs fully contained in the cloud workspace.
What e mail safety can study from the endpoint
Within the endpoint world, the breakthrough wasn’t a greater blacklist. It was the belief that prevention have to be paired with steady visibility and quick, automated response. EDR platforms gave us the flexibility to report course of timber, registry adjustments, and community calls. When a menace was detected, a bunch could possibly be remoted and adjustments could possibly be rolled again, all from a single console.
Now think about giving e mail directors the identical tremendous‑powers: a rewind button for messages, OAuth scopes and file shares; the flexibility to freeze—or a minimum of MFA‑problem—a mailbox the moment a dangerous rule is created; and a timeline that reveals who learn which delicate thread after credentials had been stolen.
This mixture of capabilities is what a contemporary, EDR-like strategy to e mail safety offers. It is a easy thought: assume an attacker will ultimately land in a mailbox and construct the tooling wanted to detect, examine, and comprise the fallout.
The API-first second that made it attainable
For years, including post-delivery controls to e mail required fragile journaling configurations or heavyweight endpoint brokers. The cloud suites quietly solved this downside for us.
Microsoft Graph and Google’s Workspace APIs now expose the required telemetry—mailbox audit logs, message IDs, sharing occasions, and permission adjustments—securely over OAuth. The identical APIs that present visibility additionally present management. They’ll revoke a token, pull a delivered message from each inbox, or take away a forwarding rule in seconds.
The sensors and the actuators are already baked into the platform. We simply want to attach them to a workflow that seems like EDR. As we have argued in our put up, The Evolution of E mail Safety, this richness of telemetry is what permits safety groups to maneuver past the whack-a-mole of tuning filter guidelines. As a substitute of ready for a consumer to report a phish, the platform can discover an impossible-travel sign-in, see that the account instantly created 5 new sharing hyperlinks, and routinely remediate the chance.
Why this issues for lean safety groups
A Director of Safety at a small and even mid-size firm is commonly your entire safety division, juggling vulnerability administration, incident response, and compliance. Device sprawl is the enemy.
An EDR-like strategy to e mail collapses a number of fragmented controls—SEG coverage, DLP, incident response playbooks, SaaS-to-SaaS monitoring—right into a single floor. There are not any MX report adjustments, no brokers to deploy, and no dependency on customers clicking a “report phish” button.
Extra importantly, it produces metrics that matter. As a substitute of citing an arbitrary “catch price,” you’ll be able to reply board-level questions with concrete knowledge:
- How shortly can we detect a compromised mailbox?
- How a lot delicate knowledge was accessible earlier than containment?
- What number of dangerous OAuth grants had been revoked this quarter?
These numbers describe precise threat discount, not theoretical filter efficacy.
A realistic strategy to transfer ahead
This does not should be an summary train. The trail ahead is incremental, and every step offers a tangible safety profit.
- Allow native audit logs. Each Microsoft 365 and Google Workspace embody in depth logging. That is the bottom reality you will want for any future automation.
- Centralize your telemetry. In your SIEM or log platform, begin in search of alerts of compromise: sudden mail rule creation, mass file downloads, uncommon sign-in places, and new OAuth grants.
- Check automated response. Use the native APIs to check “message clawback” with a phishing simulation. Each Microsoft Graph and the Gmail API provide these endpoints out of the field.
- Consider devoted platforms. Decide them on their breadth of protection, the sophistication of their post-compromise playbooks, and the velocity between detection and automatic motion.
This journey turns guesswork into proof, a reside breach right into a contained incident, and retains the human effort required proportional to your workforce’s dimension.
The underside line
Nobody in 2025 would argue that endpoint antivirus is enough by itself. We assume prevention will ultimately be bypassed, so we construct for detection and response. E mail deserves the identical pragmatic strategy.
In fact inbound detection stays crucial. But when your safety stack cannot additionally let you know who learn a delicate contract after a mailbox takeover or stop that publicity routinely then you might be nonetheless working within the antivirus period. The attackers have moved on. Your inbox, like your laptop computer, is prepared for an improve.
The place Materials Safety matches in
Materials Safety was constructed on the premise we have explored right here: e mail is a dynamic, high-value setting that wants post-delivery defenses, not simply one other pre-delivery filter.
As a result of Materials integrates instantly with Microsoft 365 and Google Workspace by way of their native APIs, deployment takes hours, not months, with no disruption to mail movement.
As soon as related, Materials information the identical positive‑grained telemetry that powers EDR on the endpoint—each mailbox rule, OAuth grant, file share, and signal‑in occasion—then layers on automated playbooks that shrink a breach window from days to minutes. A suspicious signal‑in can set off a simply‑in‑time MFA problem, whereas delivered phish are clawed again throughout each inbox earlier than they’re even learn. Historic mail is wrapped in zero‑information encryption that forces re‑authentication, so stolen credentials alone cannot unlock years of delicate knowledge.
Maybe most significantly for safety groups of 1, Materials folds these controls right into a single, searchable timeline. You may reply board‑stage questions—What was accessed? Who noticed it? How shortly did we comprise it?—with out stitching collectively half a dozen logs.
Briefly, Materials brings the “assume breach, detect quick, reply quicker” ethos of recent endpoint protection to the inbox, turning e mail from a perennial blind spot into a totally monitored, quickly recoverable asset.