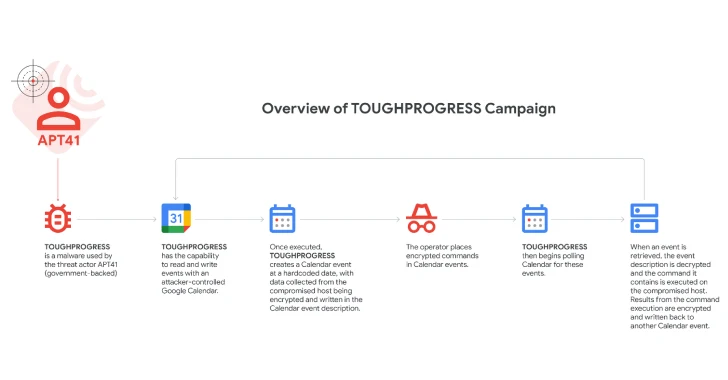
Google on Wednesday disclosed that the Chinese language state-sponsored menace actor often called APT41 leveraged a malware known as TOUGHPROGRESS that makes use of Google Calendar for command-and-control (C2).
The tech big, which found the exercise in late October 2024, stated the malware was hosted on a compromised authorities web site and was used to focus on a number of different authorities entities.
“Misuse of cloud providers for C2 is a method that many menace actors leverage so as to mix in with professional exercise,” Google Risk Intelligence Group (GTIG) researcher Patrick Whitsell stated.
APT41, additionally tracked as Axiom, Blackfly, Brass Hurricane (previously Barium), Bronze Atlas, Earth Baku, HOODOO, Pink Kelpie, TA415, Depraved Panda, and Winnti, is the identify assigned to a prolific nation-state group identified for its focusing on of governments and organizations inside the international delivery and logistics, media and leisure, expertise, and automotive sectors.
In July 2024, Google revealed that a number of entities working inside these trade verticals in Italy, Spain, Taiwan, Thailand, Turkey, and the U.Okay. have been focused by a “sustained marketing campaign” utilizing a mix of net shells and droppers like ANTSWORD, BLUEBEAM, DUSTPAN, and DUSTTRAP.
Then earlier this 12 months, a sub-cluster inside the APT41 umbrella was recognized as attacking Japanese firms within the manufacturing, supplies, and vitality sectors in March 2024 as a part of a marketing campaign dubbed RevivalStone.
The newest assault chain documented by Google entails sending spear-phishing emails containing a hyperlink to a ZIP archive that is hosted on the exploited authorities web site. The ZIP file features a listing and a Home windows shortcut (LNK) that masquerades as a PDF doc. The listing options what look like seven completely different photos of arthropods (from “1.jpg” to “7.jpg”).
The an infection begins when the LNK file is launched, inflicting a decoy PDF to be introduced to the recipient stating the species pulled from the listing must be declared for export. Nonetheless, it is price noting that “6.jpg” and “7.jpg” are faux photos.
“The primary file is definitely an encrypted payload and is decrypted by the second file, which is a DLL file launched when the goal clicks the LNK,” Whitsell stated, including the malware implements numerous stealth and evasion strategies, corresponding to memory-only payloads, encryption, compression, and management circulate obfuscation.
The malware consists of three distinct parts, every of that are deployed in collection and are designed to hold out a selected operate –
- PLUSDROP, the DLL used to decrypt and execute the next-stage in reminiscence
- PLUSINJECT, which launches and performs course of hollowing on a professional “svchost.exe” course of to inject the ultimate payload
- TOUGHPROGRESS, the first malware that makes use of Google Calendar for C2
The malware is designed to learn and write occasions with an attacker-controlled Google Calendar, making a zero-minute occasion at a hard-coded date (2023-05-30) so as to retailer the harvested information within the occasion description.
The operators place encrypted instructions in Calendar occasions on July 30 and 31, 2023, that are then polled by the malware, decrypted, executed on the compromised Home windows host, and the outcomes written again to a different Calendar occasion from the place they are often extracted by the attackers.
Google stated it has taken the step of taking down the malicious Google Calendar and terminated the related Workspace initiatives, thereby neutralizing the entire marketing campaign. It additionally stated that affected organizations have been notified. The precise scale of the marketing campaign is unclear.
This isn’t the primary time APT41 has weaponized Google’s providers to its benefit. In April 2023, Google disclosed that the menace actor focused an unnamed Taiwanese media group to ship a Go-based open-source pink teaming instrument often called Google Command and Management (GC2) delivered by way of password-protected information hosted on Google Drive.
As soon as put in, GC2 acts as a backdoor to learn instructions from Google Sheets and exfiltrate information utilizing the cloud storage service.