Are your net privateness controls defending your customers, or only a box-ticking train? This CISO’s information offers a sensible roadmap for steady net privateness validation that is aligned with real-world practices.
– Obtain the total information right here.
Internet Privateness: From Authorized Requirement to Enterprise Important
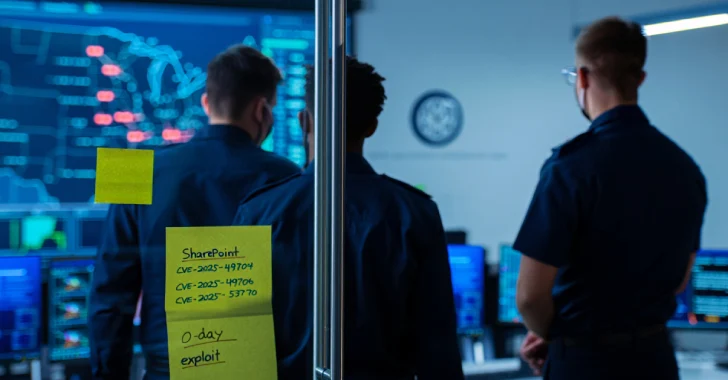
As regulators ramp up enforcement and customers develop extra privacy-aware, CISOs face a mounting problem: guaranteeing that what their group says about privateness matches what their digital property are doing.
70% of prime US web sites nonetheless drop promoting cookies even when customers choose out, a transparent contradiction of privateness claims. This hole exposes organizations to compliance failures, reputational harm, and person mistrust.
A Sensible Method to Internet Privateness Validation
Drawing from real-world incidents and regulatory tendencies, this information outlines how CISOs can combine steady privateness validation into their safety operations and explains why it is turning into a foundational follow.
Reactive vs Proactive Internet Privateness Applications
Most privateness packages depend on static audits and ineffective cookie banners, however these are poorly suited to right now’s dynamic net. The fashionable net has made these strategies out of date and elevated the position of steady monitoring—it is now important for sustaining regulatory compliance.
Reliance on the outdated reactive method results in silent privateness drift, which may set off:
- Unauthorized information assortment: For instance, a brand new advertising and marketing pixel silently gathering person IDs, or a third-party script monitoring habits that strays outdoors of the acknowledged coverage.
- Damaged consent mechanisms: Cookie consent that resets after updates, or embedded content material dropping cookies earlier than the person consents.
- Non-compliance: A kind replace unintentionally gathering additional, undisclosed private information; an AI chatbot processing queries with out the required transparency.
- Model harm: Customers noticing an surprising widget accessing location information with out their clear consent.
The takeaway: Privateness dangers are hiding in plain sight. A proactive method is extra more likely to hunt them down earlier than any harm is completed.
Reactive vs Proactive Privateness Applications: Situation Comparability
| Facet/ Situation | Reactive Privateness Program (Conventional) | Proactive Privateness Program (Steady Validation) |
| Method | Periodic, handbook audits and static compliance checks. | Steady, automated monitoring and validation in manufacturing. |
| Detection of New Dangers | New scripts, distributors, or third-party instruments could go unnoticed for months. | Each web page load and code change is scanned for brand new trackers/scripts. |
| Time to Discovery | Weeks or months—usually solely discovered after person complaints or a regulator inquiry. | Minutes or hours—automated alert triggers fast investigation. |
| Regulatory Threat | Excessive: Undetected points can result in main fines and investigations. | Low: Points are caught early, lowering publicity and demonstrating diligence. |
| Remediation Validation | Fixes are assumed to work, however hardly ever verified in manufacturing. | Automated validation confirms that remediations are efficient. |
| Useful resource Effectivity | Excessive handbook effort, vulnerable to oversight (points might be missed) and burnout. | Automated workflows release groups for higher-value duties. |
| Adaptation to New Rules | Scrambles to maintain up; typically enjoying catch-up with new legal guidelines and frameworks. | Agile response; steady validation meets evolving necessities. |
Situation Walkthrough: The Leaky Script
| Step | Reactive Program | Proactive Program |
| Script added to web site | No fast detection | Detected immediately as a brand new third-party factor. |
| Knowledge leakage begins | Continues for months, typically unnoticed. | Alert issued; information circulation flagged as coverage violation. |
| Discovery | Found solely after complaints or regulatory inquiry. | Privateness staff investigates inside hours of the alert. |
| Response | Scramble to include, examine, and report; faces regulatory fines. | Concern remediated rapidly, minimizing publicity and danger. |
| End result | €4.5M wonderful, public backlash, lack of belief. | No wonderful, incident averted, belief preserved. |
Obtain the total CISO’s information right here.
What Is Web site Privateness Validation?
Web site Privateness Validation instruments shift privateness from reactive to proactive by repeatedly monitoring your web sites, functions, and third-party code dwell in manufacturing. This ensures that your real-world exercise aligns along with your declared insurance policies.
Key capabilities: Steady Knowledge Mapping, Coverage Matching, Instantaneous Alerts, Repair Validation, and Dashboard Oversight.
Why Steady Validation Is the New Commonplace
Solely 20% of corporations really feel assured of their privateness compliance, however steady validation removes doubt. It strengthens compliance, simplifies audits, and integrates into present safety workflows, due to agentless deployment of some distributors that minimizes operational overhead.
Case in Level: The Value of Inaction
A world retailer launched a loyalty program, however unknown to them, it included a third-party script that was sending buyer emails to an exterior area. This went undetected for 4 months and ultimately led to a €4.5 million wonderful, public backlash, and a lack of govt belief. With privateness validation, the problem might have been resolved in hours, not months, and all that costly fallout might have been prevented.
Very like the worldwide retailer, suppliers in each the healthcare and monetary providers industries have opened themselves as much as critical repercussions after failing to proactively validate net privateness. As an example, a hospital community uncared for to validate the third-party analytics scripts operating on its web site, which left them free to silently accumulate affected person information with out consent. This violated HIPAA laws, risked fines, and broken affected person belief.
Equally, a financial institution suffered an information breach when a third-party vendor added a monitoring script that accessed delicate account info with out correct authorization. In each instances, net privateness validation might have instantly flagged these points, stopping unauthorized information assortment, avoiding authorized repercussions, and preserving buyer belief throughout these extremely regulated sectors.
Get Prepared for 2025’s Harder Rules
New frameworks just like the EU AI Act and New Hampshire’s NHPA are altering how organizations method privateness. CISOs now face unprecedented validation necessities, together with:
- Complete AI danger assessments with steady algorithm transparency
- Superior consent mechanisms that dynamically reply to alerts like International Privateness Management
- Rigorous safeguards for delicate information processing throughout all digital touchpoints
- Obligatory documentation and technical validation of privateness controls
- Cross-border information switch mechanisms that stand up to growing scrutiny
The regulatory panorama is not simply evolving—it is accelerating, so organizations that implement steady net privateness validation now will likely be strategically positioned to navigate these advanced necessities whereas their rivals are scrambling to catch up.
Do not Watch for a Violation Earlier than You Take Motion
Discover actionable steps and real-world examples within the full CISO’s Information to Internet Privateness Validation.
→ Obtain the total CISO’s Information to Internet Privateness Validation right here.