Cybersecurity researchers have disclosed a malware marketing campaign that makes use of pretend software program installers masquerading as common instruments like LetsVPN and QQ Browser to ship the Winos 4.0 framework.
The marketing campaign, first detected by Rapid7 in February 2025, entails the usage of a multi-stage, memory-resident loader known as Catena.
“Catena makes use of embedded shellcode and configuration switching logic to stage payloads like Winos 4.0 totally in reminiscence, evading conventional antivirus instruments,” safety researchers Anna Širokova and Ivan Feigl stated. “As soon as put in, it quietly connects to attacker-controlled servers – principally hosted in Hong Kong – to obtain follow-up directions or further malware.”
The assaults, like those who have deployed Winos 4.0 prior to now, seem to focus particularly on Chinese language-speaking environments, with the cybersecurity firm calling out the “cautious, long-term planning” by a really succesful menace actor.
Winos 4.0 (aka ValleyRAT) was first publicly documented by Pattern Micro in June 2024 as utilized in assaults concentrating on Chinese language-speaking customers by way of malicious Home windows Installer (MSI) recordsdata for VPN apps. The exercise has been attributed to a menace cluster it tracks as Void Arachne, which can be known as Silver Fox.
Subsequent campaigns distributing the malware have leveraged gaming-related functions like set up instruments, velocity boosters, and optimization utilities as lures to trick customers into putting in it. One other assault wave detailed in February 2025 focused entities in Taiwan through phishing emails that presupposed to be from the Nationwide Taxation Bureau.
Constructed atop the foundations of a identified distant entry trojan known as Gh0st RAT, Winos 4.0 is a sophisticated malicious framework written in C++ that makes use of a plugin-based system to reap information, present distant shell entry, and launch distributed denial-of-service (DDoS) assaults.
 |
| QQBrowser-Based mostly An infection Movement Noticed in February 2025 |
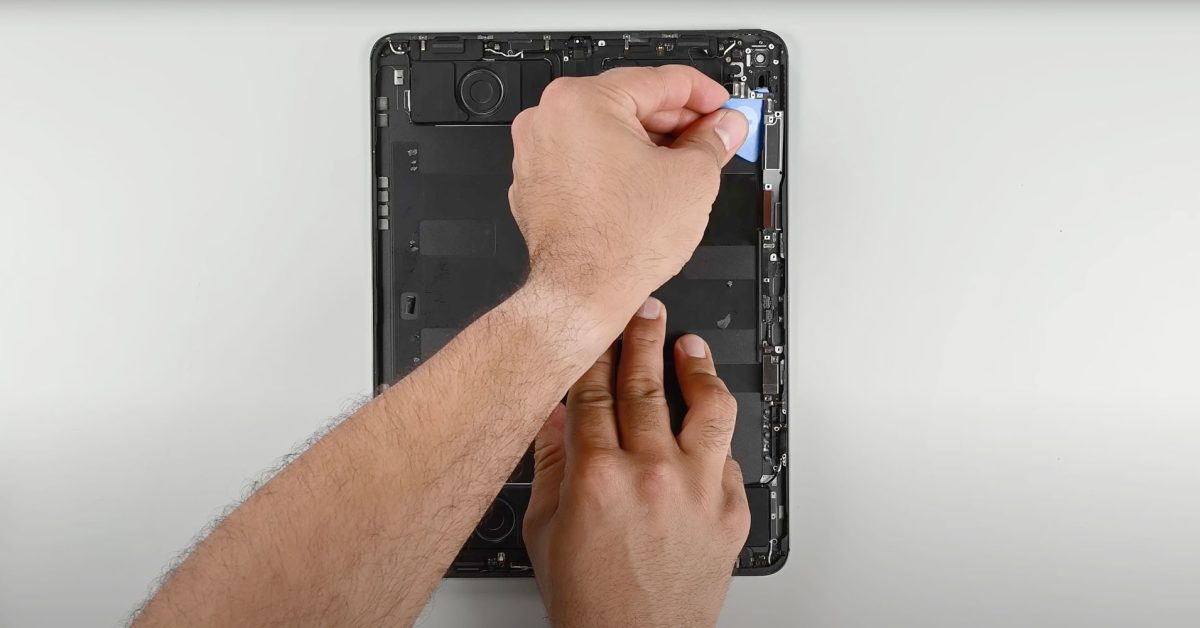
Rapid7 stated all of the artifacts flagged in February 2025 relied on NSIS installers bundled with signed decoy apps, shellcode embedded in “.ini” recordsdata, and reflective DLL injection to covertly preserve persistence on contaminated hosts and keep away from detection. Your complete an infection chain has been given the moniker Catena.
“The marketing campaign has to this point been lively all through 2025, displaying a constant an infection chain with some tactical changes – pointing to a succesful and adaptive menace actor,” the researchers stated.
The place to begin is a trojanized NSIS installer impersonating an installer for QQ Browser, a Chromium-based internet browser developed by Tencent, that is designed to ship Winos 4.0 utilizing Catena. The malware communicates with hard-coded command-and-control (C2) infrastructure over TCP port 18856 and HTTPS port 443.
 |
| From LetsVPN Installer to Winos 4.0 in April 2025 |
Persistence on the host is achieved by registering scheduled duties which might be executed weeks after the preliminary compromise. Whereas the malware options an express test to search for Chinese language language settings on the system, it nonetheless proceeds with the execution even when that is not the case.
This means it is an unfinished function and one thing that is anticipated to be carried out in subsequent iterations of the malware. That stated, Rapid7 stated it recognized in April 2025 a “tactical shift” that not solely switched among the components of the Catena execution chain, but in addition included options to evade antivirus detection.
Within the revamped assault sequence, the NSIS installer disguises itself as a setup file for LetsVPN and runs a PowerShell command that provides Microsoft Defender exclusions for all drives (C: to Z:). It then drops further payloads, together with an executable that takes a snapshot of operating processes and checks for processes associated to 360 Complete Safety, an antivirus product developed by Chinese language vendor Qihoo 360.
The binary is signed with an expired certificates issued by VeriSign and allegedly belongs to Tencent Expertise (Shenzhen). It was legitimate from 2018-10-11 to 2020-02-02. The first duty of the executable is to reflectively load a DLL file that, in flip, connects to a C2 server (“134.122.204[.]11:18852” or “103.46.185[.]44:443”) in an effort to obtain and execute Winos 4.0.
“This marketing campaign exhibits a well-organized, regionally centered malware operation utilizing trojanized NSIS installers to quietly drop the Winos 4.0 stager,” the researchers stated.
“It leans closely on memory-resident payloads, reflective DLL loading, and decoy software program signed with legit certificates to keep away from elevating alarms. Infrastructure overlaps and language-based concentrating on trace at ties to Silver Fox APT, with exercise seemingly aimed toward Chinese language-speaking environments.”