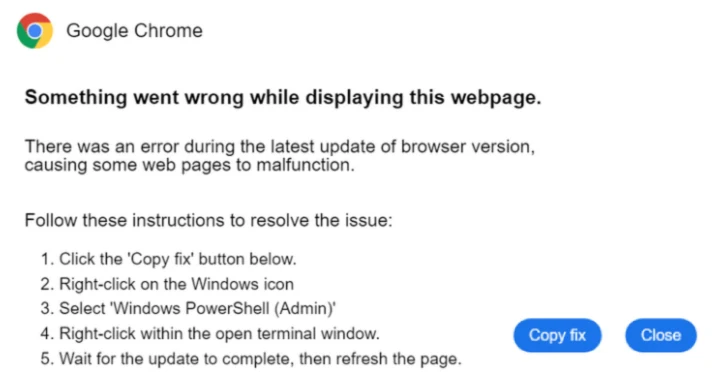
The malware often called Latrodectus has develop into the most recent to embrace the widely-used social engineering approach referred to as ClickFix as a distribution vector.
“The ClickFix approach is especially dangerous as a result of it permits the malware to execute in reminiscence quite than being written to disk,” Expel mentioned in a report shared with The Hacker Information. “This removes many alternatives for browsers or safety instruments to detect or block the malware.”
Latrodectus, believed to be a successor to IcedID, is the title given to a malware that acts as a downloader for different payloads, resembling ransomware. It was first documented by Proofpoint and Crew Cymru in April 2024.
By the way, the malware is one among the many many malicious software program to endure an operational setback as a part of Operation Endgame, which took down 300 servers worldwide and neutralized 650 domains associated to Bumblebee, Lactrodectus, QakBot, HijackLoader, DanaBot, TrickBot, and WARMCOOKIE between Might 19 and 22, 2025.
Within the newest set of Latrodectus assaults noticed by Expel in Might 2025, unsuspecting customers are tricked into copying and executing a PowerShell command from an contaminated web site, a tactic that has develop into a prevalent methodology to distribute a variety of malware.
“When run by a consumer, these instructions will try to put in a file situated on the distant URL utilizing MSIExec, after which execute it in reminiscence,” Expel mentioned. “This retains the attacker from having to put in writing the file to the pc and threat being detected by the browser or an antivirus which may detect it on disk.”
The MSI installer comprises a authentic software from NVIDIA, which is used to sideload a malicious DLL, which then makes use of curl to obtain the principle payload.
To mitigate assaults of this sort, it is suggested to disable the Home windows Run program utilizing Group Coverage Objects (GPOs) or flip off the “Home windows + R” sizzling key through a Home windows Registry change.
From ClickFix to TikTok
The disclosure comes as Pattern Micro revealed particulars of a brand new engineering marketing campaign that as an alternative of counting on faux CAPTCHA pages employs TikTok movies doubtless generated utilizing synthetic intelligence (AI) instruments to ship the Vidar and StealC info stealers by instructing customers to run malicious instructions on their programs to activate Home windows, Microsoft Workplace, CapCut, and Spotify.
These movies have been posted from varied TikTok accounts resembling @gitallowed, @zane.houghton, @allaivo2, @sysglow.wow, @alexfixpc, and @digitaldreams771. These accounts are now not lively. One of many movies claiming to supply directions on “increase your Spotify expertise immediately” has amassed practically 500,000 views, with over 20,000 likes and greater than 100 feedback.
The marketing campaign marks a brand new escalation of ClickFix in that customers trying to find methods to activate pirated apps are verbally and visually guided to open the Home windows Run dialog by urgent the “Home windows + R” sizzling key, launch PowerShell, and run the command highlighted within the video, finally compromising their very own programs.
“Risk actors are actually utilizing TikTok movies which are doubtlessly generated utilizing AI-powered instruments to socially engineer customers into executing PowerShell instructions beneath the guise of guiding them to activate authentic software program or unlock premium options,” safety researcher Junestherry Dela Cruz mentioned.
“This marketing campaign highlights how attackers are able to weaponize whichever social media platforms are at the moment in style to distribute malware.”
Pretend Ledger Apps Used to Steal Mac Customers’ Seed Phrases
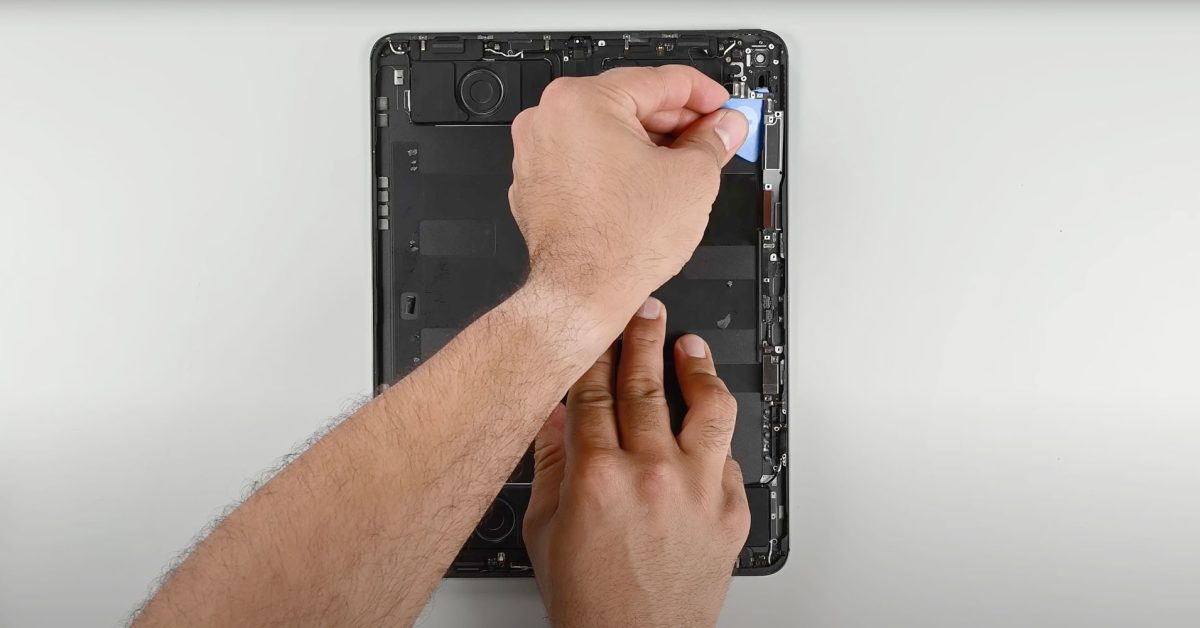
The findings additionally observe the invention of 4 totally different malware campaigns that leverage a cloned model of the Ledger Stay app to steal delicate knowledge, together with seed phrases, with the aim of draining victims’ cryptocurrency wallets. The exercise has been ongoing since August 2024.
The assaults make use of the malicious DMG information that, when launched, launches AppleScript to exfiltrate passwords and Apple Notes knowledge, after which obtain a trojanized model of Ledger Stay. As soon as the app is opened, it warns customers of a supposed account drawback and that it requires their seed phrase for restoration. The entered seed phrase is distributed to an attacker-controlled server.
Moonlock Lab, which make clear the marketing campaign, mentioned the rogue apps make use of macOS stealer malware like Atomic macOS Stealer (AMOS) and Odyssey, the latter of which launched the novel phishing scheme in March 2025. It is value noting that the exercise overlaps with a macOS infostealer marketing campaign that targets Ledger Stay customers by PyInstaller-packed binaries, as revealed by Jamf this month.
“On darkish net boards, chatter round anti-Ledger schemes is rising. The subsequent wave is already taking form,” MacPaw’s cybersecurity division famous. “Hackers will proceed to take advantage of the belief crypto house owners place in Ledger Stay.”