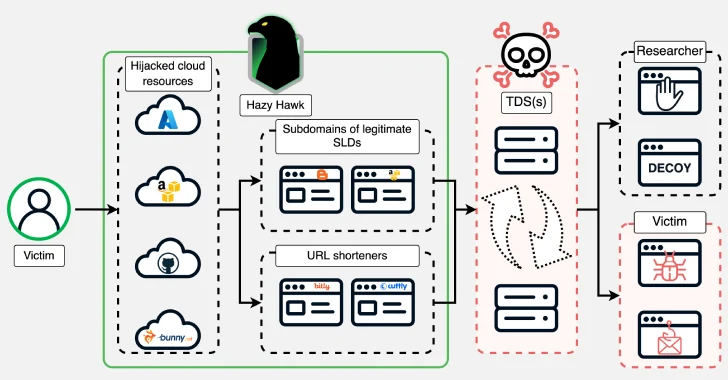
A risk actor often known as Hazy Hawk has been noticed hijacking deserted cloud assets of high-profile organizations, together with Amazon S3 buckets and Microsoft Azure endpoints, by leveraging misconfigurations within the Area Identify System (DNS) information.
The hijacked domains are then used to host URLs that direct customers to scams and malware through site visitors distribution techniques (TDSes), in line with Infoblox. A few of the different assets usurped by the risk actor embrace these hosted on Akamai, Bunny CDN, Cloudflare CDN, GitHub, and Netlify.
The DNS risk intelligence agency mentioned it first found the risk actor after it gained management of a number of sub-domains related to the U.S. Heart for Illness Management (CDC) in February 2025.
It has since been decided that different authorities businesses throughout the globe, distinguished universities, and worldwide companies corresponding to Deloitte, PricewaterhouseCoopers, and Ernst & Younger have been victimized by the identical risk actor since a minimum of December 2023.
“Maybe essentially the most outstanding factor about Hazy Hawk is that these hard-to-discover, susceptible domains with ties to esteemed organizations usually are not getting used for espionage or ‘intellectual’ cybercrime,” Infoblox’s Jacques Portal and Renée Burton mentioned in a report shared with The Hacker Information.
“As a substitute, they feed into the seedy underworld of adtech, whisking victims to a variety of scams and faux purposes, and utilizing browser notifications to set off processes that may have a lingering impression.”
What makes Hazy Hawk’s operations noteworthy is the hijacking of trusted and respected domains belonging to reliable organizations, thus boosting their credibility in search outcomes when they’re getting used to serve malicious and spammy content material. However much more concerningly, the method permits the risk actors to bypass detection.
Underpinning the operation is the flexibility of the attackers to grab management of deserted domains with dangling DNS CNAME information, a way beforehand uncovered by Guardio in early 2024 as being exploited by dangerous actors for spam proliferation and click on monetization. All a risk actor must do is register the lacking useful resource to hijack the area.
Hazy Hawk goes a step additional by discovering deserted cloud assets after which commandeering them for malicious functions. In some instances, the risk actor employs URL redirection methods to hide which cloud useful resource was hijacked.
“We use the title Hazy Hawk for this actor due to how they discover and hijack cloud assets which have dangling DNS CNAME information after which use them in malicious URL distribution,” Infoblox mentioned. “It is doable that the area hijacking element is offered as a service and is utilized by a bunch of actors.”
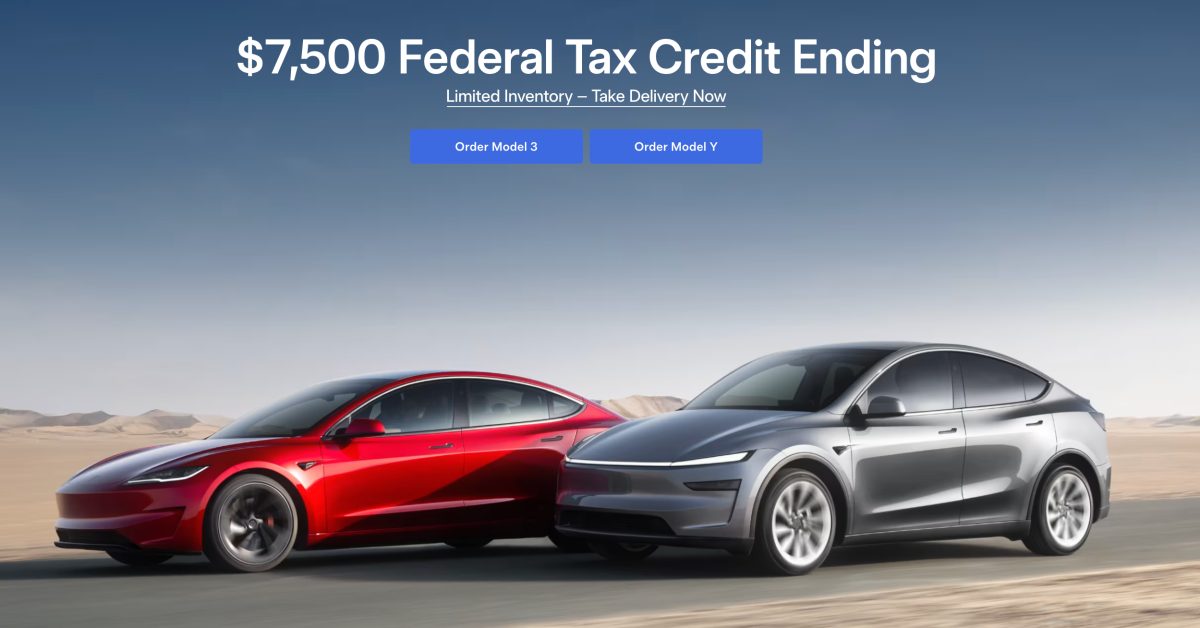
The assault chains typically contain cloning the content material of reliable websites for his or her preliminary website hosted on the hijacked domains, whereas luring victims into visiting them with pornographic or pirated content material. The location guests are then funneled through a TDS to find out the place they land subsequent.
“Hazy Hawk is likely one of the dozens of risk actors we observe inside the promoting affiliate world,” the corporate mentioned. “Menace actors who belong to affiliate promoting applications drive customers into tailor-made malicious content material and are incentivized to incorporate requests to permit push notifications from ‘web sites’ alongside the redirection path.”
In doing so, the concept is to flood a sufferer’s machine with push notifications and ship an countless torrent of malicious content material, with every notification resulting in completely different scams, scareware, and faux surveys, and accompanied by requests to permit extra push notifications.
To forestall and shield towards Hazy Hawk actions, area homeowners are advisable to take away a DNS CNAME file as quickly as a useful resource is shut down. Finish customers, however, are suggested to disclaim notification requests from web sites they do not know.
“Whereas operators like Hazy Hawk are chargeable for the preliminary lure, the consumer who clicks is led right into a labyrinth of sketchy and outright malicious adtech. The truth that Hazy Hawk places appreciable effort into finding susceptible domains after which utilizing them for rip-off operations reveals that these promoting affiliate applications are profitable sufficient to pay properly,” Infoblox mentioned.