The nation-state menace actor often called MirrorFace has been noticed deploying malware dubbed ROAMINGMOUSE as a part of a cyber espionage marketing campaign directed in opposition to authorities companies and public establishments in Japan and Taiwan.
The exercise, detected by Development Micro in March 2025, concerned using spear-phishing lures to ship an up to date model of a backdoor known as ANEL.
“The ANEL file from the 2025 marketing campaign mentioned on this weblog carried out a brand new command to help an execution of BOF (Beacon Object File) in reminiscence,” safety researcher Hara Hiroaki mentioned. “This marketing campaign additionally probably leveraged SharpHide to launch the second stage backdoor NOOPDOOR.”
The China-aligned menace actor, also referred to as Earth Kasha, is assessed to be a sub-cluster inside APT10. In March 2025, ESET shed mild on a marketing campaign known as Operation AkaiRyū that focused a diplomatic group within the European Union in August 2024 with ANEL (aka UPPERCUT).
The focusing on of varied Japanese and Taiwanese entities factors to a continued enlargement of their footprint, because the hacking crew seeks to conduct info theft to advance their strategic aims.
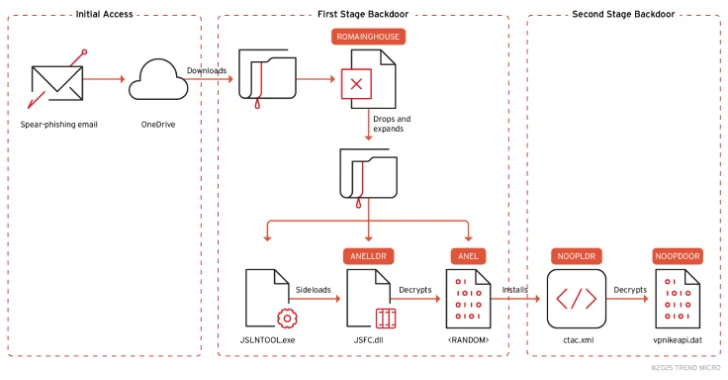
The assault begins with a spear-phishing electronic mail — a few of that are despatched from legitimate-but-compromised accounts — that incorporates an embedded Microsoft OneDrive URL, which, in flip, downloads a ZIP file.
The ZIP archive features a malware-laced Excel doc, and a macro-enabled dropper codenamed ROAMINGMOUSE that serves as a conduit to ship elements associated to ANEL. It is price noting that ROAMINGMOUSE has been put to make use of by MirrorFace since final yr.
“ROAMINGMOUSE then decodes the embedded ZIP file through the use of Base64, drops the ZIP on a disk, and expands its elements,” Hiroaki mentioned. This consists of –
- JSLNTOOL.exe, JSTIEE.exe, or JSVWMNG.exe (a official binary)
- JSFC.dll (ANELLDR)
- An encrypted ANEL payload
- MSVCR100.dll (a official DLL dependency of the executable)
The tip objective of the assault chain is to launch the official executable utilizing explorer.exe after which use it to sideload the malicious DLL, on this case, ANELLDR, which is answerable for decrypting and launching the ANEL backdoor.
What’s notable in regards to the ANEL artifact used within the 2025 marketing campaign is the addition of a brand new command to help in-memory execution of beacon object information (BOFs), that are compiled C applications designed to increase the Cobalt Strike agent with new post-exploitation options.
“After putting in the ANEL file, actors behind Earth Kasha obtained screenshots utilizing a backdoor command and examined the sufferer’s surroundings,” Development Micro defined. “The adversary seems to research the sufferer by wanting by way of screenshots, working course of lists, and area info.”
Choose cases have additionally leveraged an open-source software named SharpHide to launch a brand new model of NOOPDOOR (aka HiddenFace), one other backdoor beforehand recognized as utilized by the hacking group. The implant, for its half, helps DNS-over-HTTPS (DoH) to hide its IP deal with lookups throughout command-and-control (C2) operations.
“Earth Kasha continues to be an energetic superior persistent menace and is now focusing on authorities companies and public establishments in Taiwan and Japan in its newest marketing campaign which we detected in March 2025,” Hiroaki mentioned.
“Enterprises and organizations, particularly these with high-value property like delicate information referring to governance, in addition to mental property, infrastructure information, and entry credentials ought to proceed to be vigilant and implement proactive safety measures to stop falling sufferer to cyber assaults.”