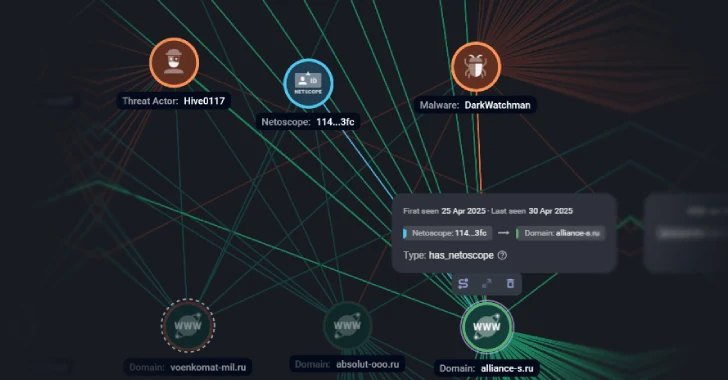
Russian firms have been focused as a part of a large-scale phishing marketing campaign that is designed to ship a recognized malware known as DarkWatchman.
Targets of the assaults embody entities within the media, tourism, finance and insurance coverage, manufacturing, retail, vitality, telecom, transport, and biotechnology sectors, Russian cybersecurity firm F6 mentioned.
The exercise is assessed to be the work of a financially motivated group known as Hive0117, which has been attributed by IBM X-Pressure to assaults aimed toward customers in Lithuania, Estonia, and Russia spanning telecom, digital, and industrial sectors.
Then in September 2023, the DarkWatchman malware was as soon as once more used in a phishing marketing campaign focusing on vitality, finance, transport, and software program safety industries primarily based in Russia, Kazakhstan, Latvia, and Estonia.
Russian banks, retailers and marketplaces, telecom operators, agro-industrial enterprises, gasoline and vitality firms, logistics companies, and IT companies had been singled out once more in November 2023 with DarkWatchman utilizing courier delivery-themed lures.
A JavaScript-based distant entry trojan, DarkWatchman is able to keylogging, accumulating system data, and deploying secondary payloads. It was first documented in December 2021.
“The fileless nature of the DarkWatchman malware, and its use of JavaScript and a keylogger written in C#, in addition to the power to take away traces of its existence on compromised techniques when instructed, are proof of considerably subtle capabilities,” IBM famous in 2023.
The most recent set of assaults includes sending phishing emails containing password-protected malicious archives that, as soon as opened, ship a variant of DarkWatchman with improved capabilities to evade detection.
Ukraine Focused by New Sheriff Backdoor
The disclosure comes as IBM X-Pressure mentioned an unspecified entity inside Ukraine’s protection sector was focused within the first half of 2024 with a beforehand undocumented Home windows backdoor known as Sheriff.
“The menace actor used a well-liked information portal in Ukraine, ukr.web, to host the Sheriff backdoor,” safety researcher Golo Mühr mentioned in a report printed in late March 2025. “The modular backdoor can execute actor-directed instructions, acquire screenshots, and covertly exfiltrate sufferer knowledge utilizing the Dropbox cloud storage API.”
“The malware focuses on exfiltrating knowledge and taking screenshots whereas sustaining a low profile designed for extended compromises.”
It is suspected that the web site might have been breached to stage the malware in early March 2024. Sheriff is provided to obtain and handle a number of parts, together with a screenshot module, with instructions and configuration values acquired as ZIP file feedback.
“A menace actor’s entry to Ukraine’s largest information portal would place them to conduct a spread of high-impact assaults and function with enhanced obfuscation,” Mühr mentioned. “On this particular incident, the menace actor might have abused the trusted area to stage malware with out elevating suspicion.”
The backdoor additionally comes fitted with a “suicide” operate that, when invoked remotely by the operator, ceases all exercise and deletes the listing containing the malware and the folder on Dropbox used for command-and-control (C2) communications.
IBM identified that sure facets of the malware overlap with that of Turla’s Kazuar and Crutch, in addition to Operation Groundbait’s Prikormka and Unhealthy Magic’s CloudWizard.
“Each CloudWizard and Sheriff comprise a operate ‘GetSettings”https://thehackernews.com/”get_Settings’ to retrieve every module’s configuration,” the corporate mentioned. “CloudWizard, Prikormka, and Sheriff share the identical screenshot taking intervals of quarter-hour. CloudWizard and Prikormka’s file itemizing modules are known as ‘tree,’ which is the title Sheriff makes use of for exfiltration of a listing of information.”
The invention of the backdoor follows a report from Ukraine’s State Service for Particular Communications and Info Safety (SSSCIP), warning of a 48% enhance within the variety of incidents within the second half of 2024 (2,576), in comparison with the earlier six-month interval (1,739).
In complete, 4,315 cyber incidents had been registered in 2024, up from 1,350 in 2021, 2,194 in 2022, and a couple of,543 in 2023. The variety of crucial and high-severity incidents, alternatively, dropped considerably to 59, a decline from 1,048 in 2022 and 367 in 2023.
“Russian hackers are actively implementing automation, using provide chain assaults for infiltration by software program distributors, and mixing espionage and sabotage methods,” SSSCIP mentioned. “The first focus of assaults is the gathering of intelligence that might affect the operational state of affairs on the entrance. Particularly, the adversary is focusing on situational consciousness techniques and specialised protection enterprises.”